47X Better Performance, Safeheron TSS-RSA Algorithm Officially Open-Source
06/25/2022
As a transparent and open source digital asset self-custody platform, Safeheron is committed to contributing to the crypto world by providing a secure, transparent, and verifiable self-custody infrastructure.
In line with this principle, Safeheron has been continuously committed to open-source development.
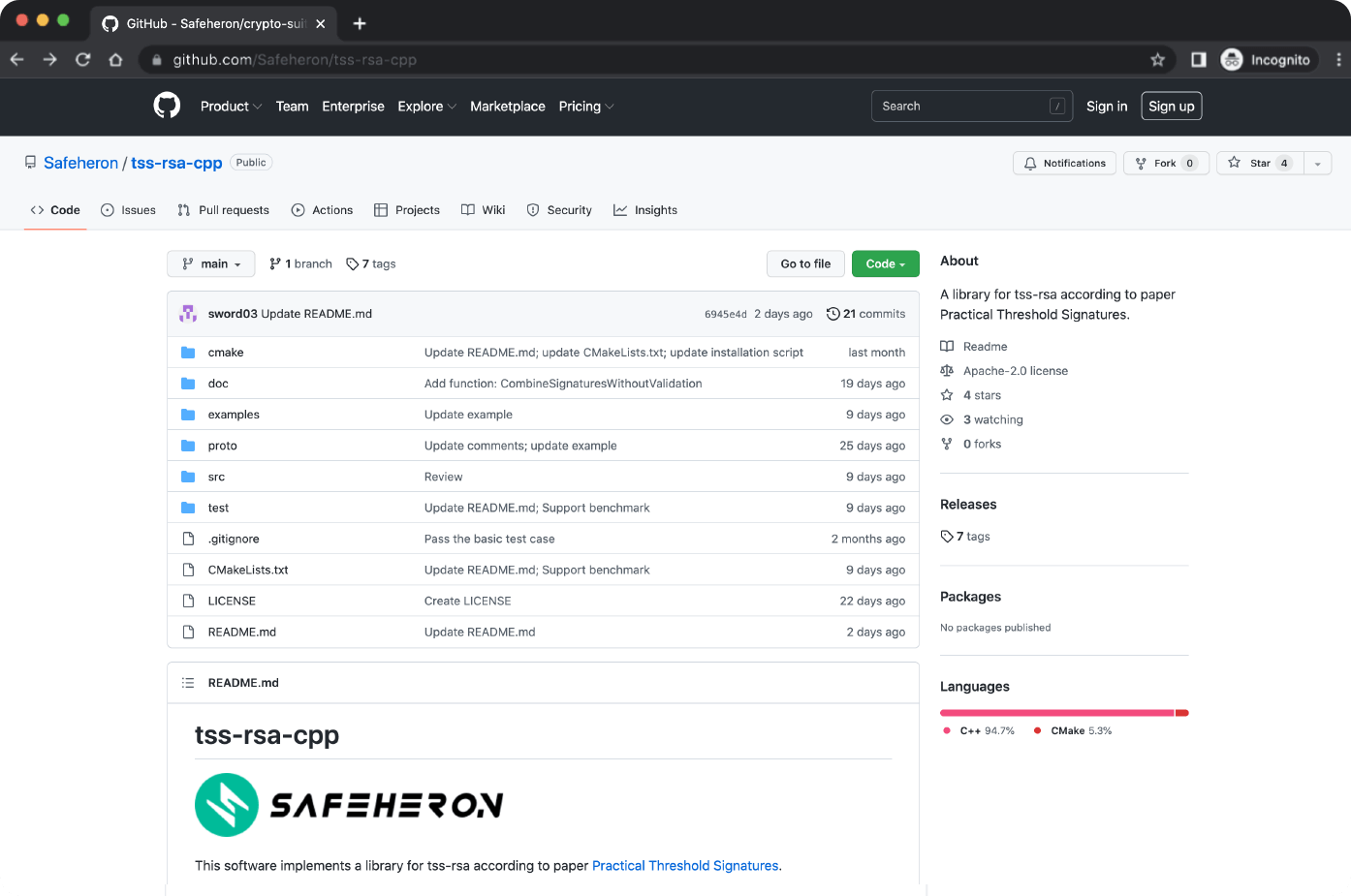
Recently, based on the paper, Practical Threshold Signatures, Safeheron implemented and open-sourced the TSS-RSA (Threshold Signature Scheme of RSA) algorithm library and established in-depth cooperation with Arweave’s project, everFinance.
GitHub
TSS-RSA Algorithm
Threshold Signature Scheme is a distributed multi-party signing protocol that contains distributed key generation, signing and verification algorithms. For example, in a (2, 3) threshold scheme, the threshold is 3 which is 3 users co-manage one private key. Everyone only holds part of the key shard while the rest shard won’t be publicly exposed. When signing a transaction, we need to combine at least 2 users’ signature data into one valid signature.
TSS-RSA is an RSA-based threshold signature algorithm implemented by C++. Compared to the traditional threshold signature, TSS-RSA has the following advantages:
It is based on RSA problem.
Signature shard generation and verification are completely non-interactive.
The signature content size of a single private key shard will be smaller.
Besides, compared to traditional multisignature, TSS-RSA generates no more signature data than multi-signature. Transactions using TSS-RSA only have one signature data, so the transaction processing fees (sometimes called miner fees, transaction fees, or gas fees) paid to miners can be kept to a minimum. Also, the responsibility of key generation and key management is distributed to multiple parties, thus, the risk of a single private key is securely eliminated.
TSS-RSA Library Functionality And Usage
Based on OpenSSL, Protocol Buffers, and crypto-suites-cpp open-source libraries, the Safeheron TSS-RSA library implements automatic compiling by Cmake. Now, it supports running on Linux and macOS. crypto-suites-cpp is a cryptography repository developed by Safeheron, which contains big number computation, elliptic curve algorithm, commitment scheme, hash algorithm, key sharing protocol, Paillier homomorphic encryption algorithm, zero-knowledge protocol, BIP32 derivation protocol, elliptic curve public key cryptography ECIES (standard IEEE 1363a compatible) and other cryptography suites.
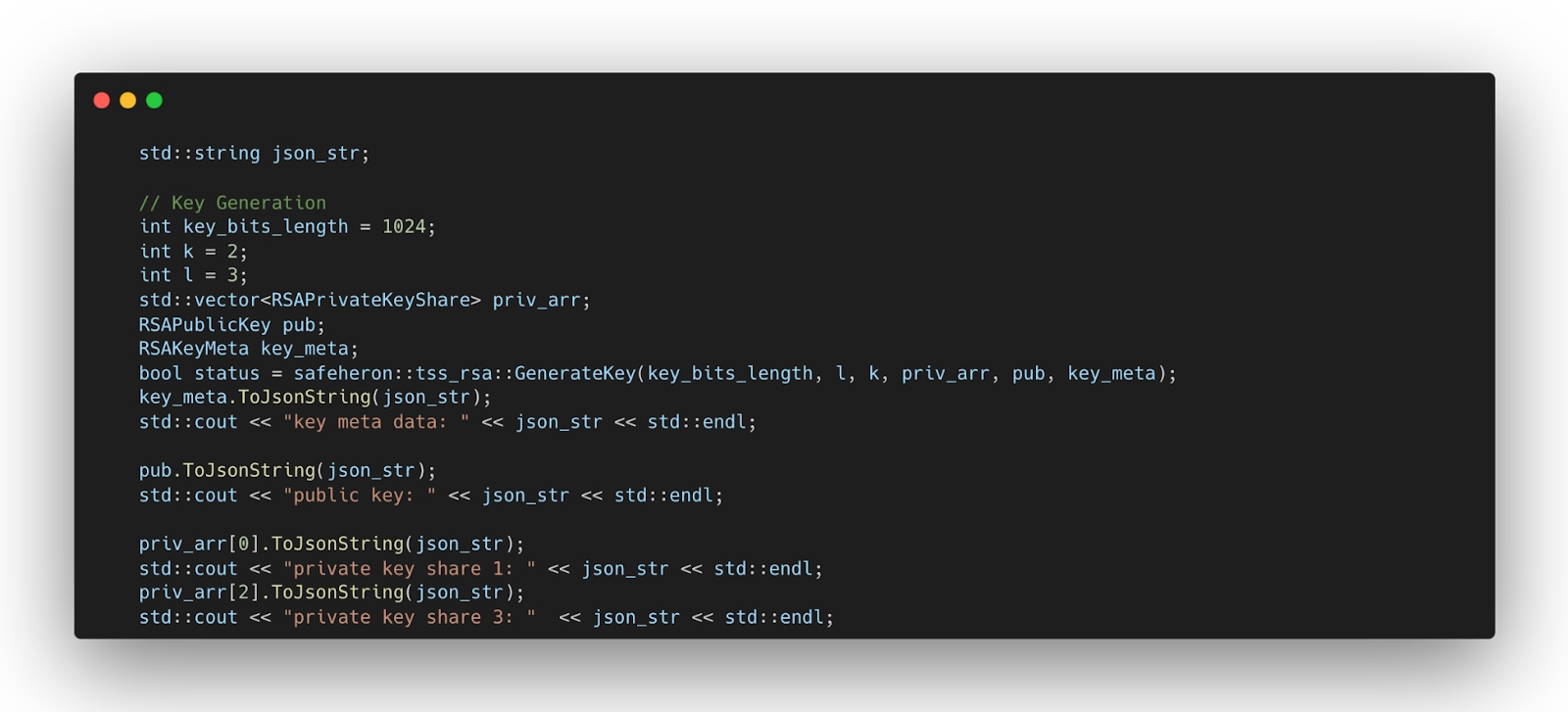
There are four function modules, which are key shard generation, signature shard generation, signature shard combination, and signature verification.
Key Shard Generation
Before generating a private key shard, you need to set initialization parameters and then call GenerateKey to generate a private key shard.
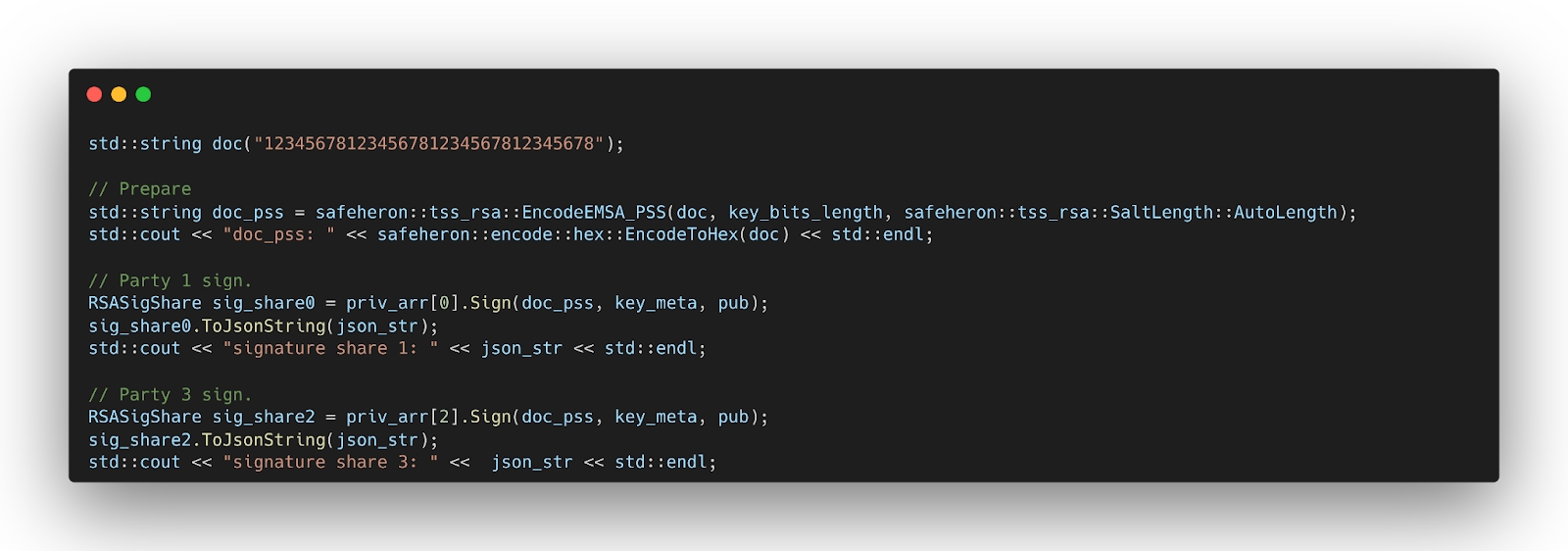
Signature Shard Generation
Use the EncodeEMSA_PSS to preprocess the message, then use the generated private key shard to sign the preprocessed message, and generate a signature shard with a correctness certificate for the signature shard.
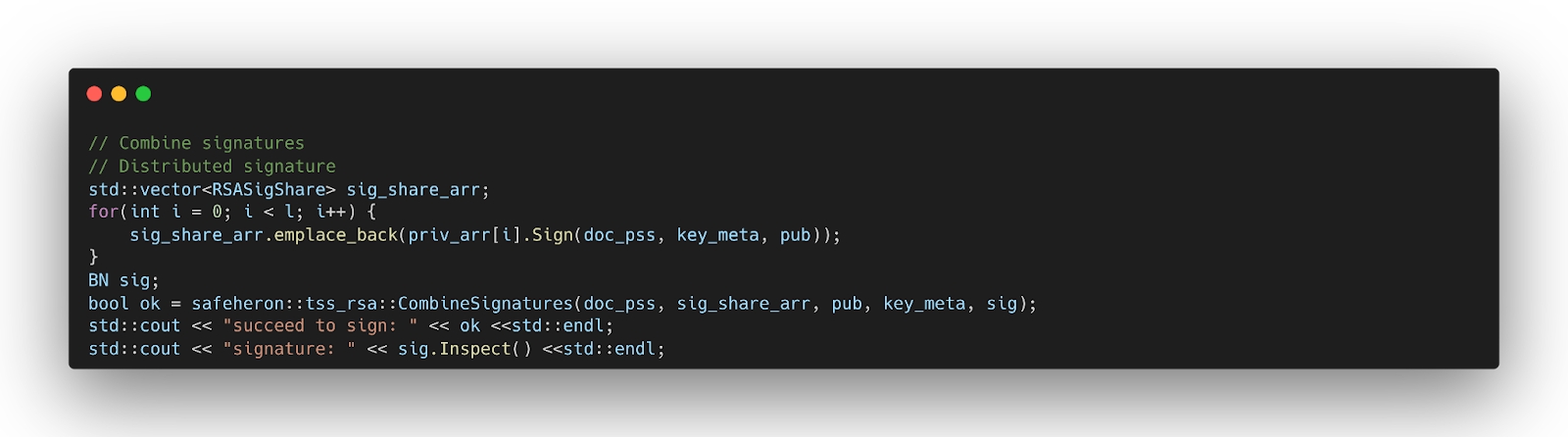
Signature Shard Combination
Call CombineSignatures to combine the generated signature shards.
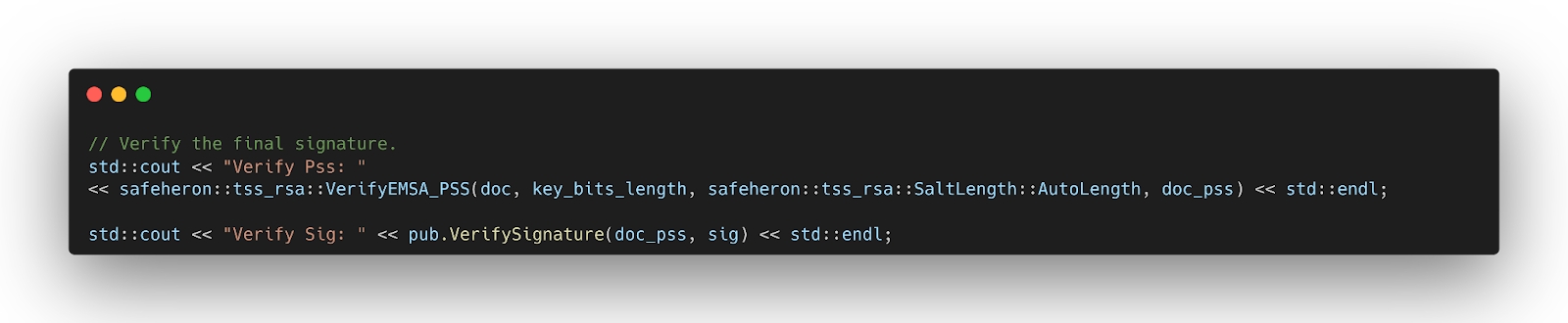
Signature Verification
Call VerifyEMSA_PSS to verify the integrity of the signature. And then, verify the correctness of the signature via VerifySignature. The verification is consistent with the standard RSA algorithm.
The output can be seen at
Safeheron TSS-RSA Performance
TCRSA, the open-source project developed by Golang is another implementation of Practical Threshold Signatures, but the efficiency is not quite satisfying.
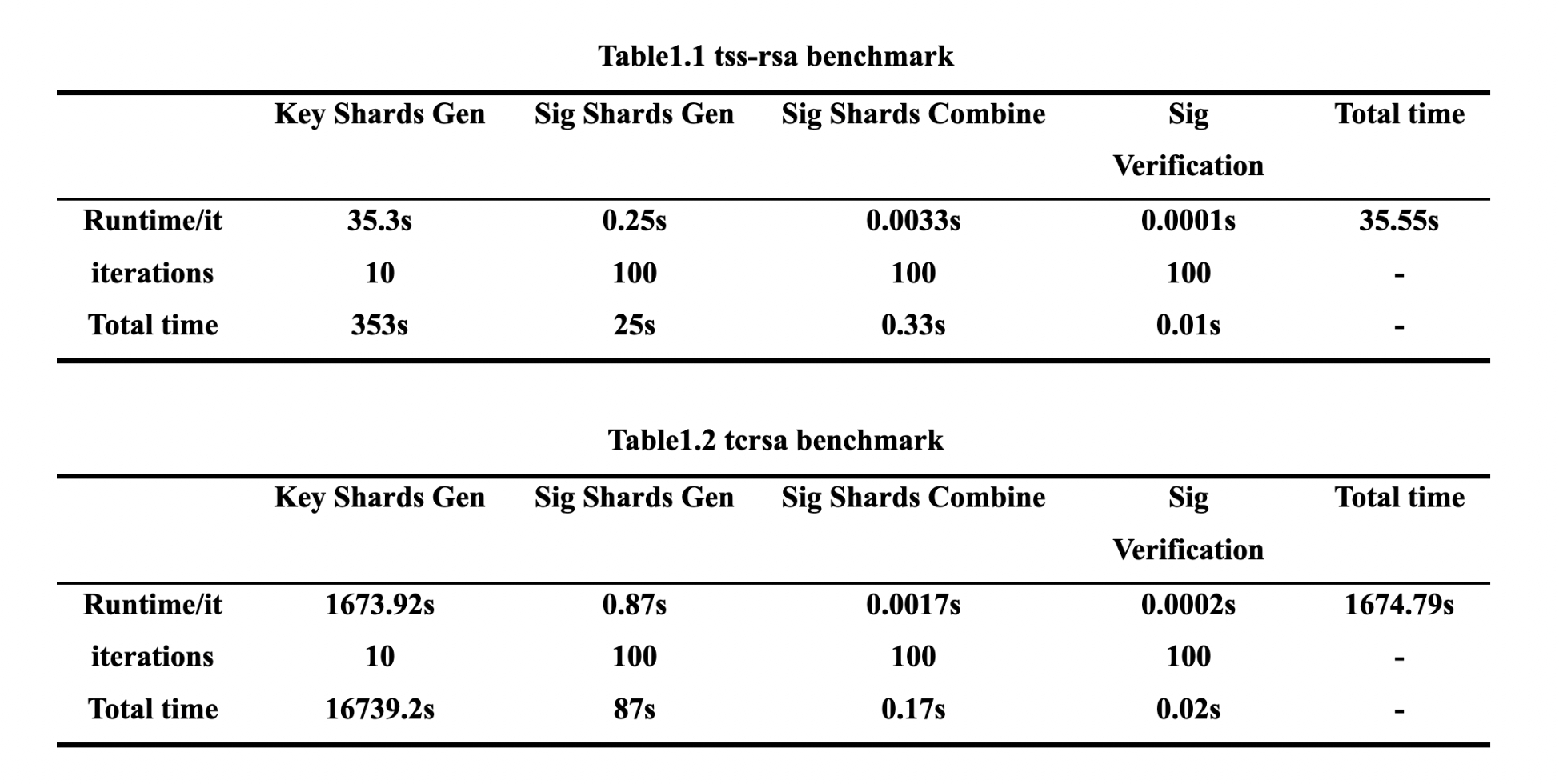
To identify the efficiency differences between TSS-RSA and TCRSA, Safeheron took Benchmark testing, and compared and analyzed the above four function modules.
See the result below:
Runtime Environment: os: linux,arch: amd64,cpu: 2 X 2499.99 MHz
Parameters Initialization: n (RSA-module bits) = 4096, L(participants counter) = 5, K(threshold) = 3
Comparing the above two tables, it can be seen that when the runtime environment and parameter values are the same, the efficiency of the TSS-RSA and TCRSA libraries is mainly reflected by the process of generating private key shards. For TSS-RSA, it only takes 35.3s to perform one round of private key shards generation, while TCRSA needs 1673.92s, which is about 47.4 times slower than the former. Further, the signature shard generation of TSS-RSA is also about 2.5 times faster than that of TCRSA.
Overall, it takes a total of 35.55s for TSS-RSA to perform a complete signature generation and verification, and 1674.79s for TCRSA to complete the same process. We can see that the time TCRSA required is about 47 times as long as TSS-RSA required.
What's Coming...
Safeheron has built a strategic partnership with Arweave’s financial infrastructure everPay (everFinance) . Safeheron will soon launch the TEE-Based RSA Key Sharding Service to be the solid and strong security infrastructure for the everPay and the whole Arweave ecosystem.
Safeheron’s TEE-Based RSA Key Sharding Service adopts the SGX confidential computing technology provided by Intel CPU hardware and solves the potential security problem of centralized generation of RSA keys by running the entire process of key generation and sharding of TSS-RSA (Threshold Signature Scheme of RSA) algorithm into the trusted execution environment. By this approach, the RSA key is guaranteed to be available and, only visible to the hardware encryption chip, eliminating the potential security problem of centralized RSA key generation. Based on the unique institutional-grade security solution provided by Safeheron, together with Intel's remote attestation, the entire process of key shard generation is ensured to be trustworthy and this trustworthiness is technically verifiable.
Pretty soon, Safeheron will also open source the entire trusted RSA key sharding service source code to ensure the security and trustworthiness of the system in a completely transparent way. Let’s bring better security to the blockchain ecosystem.
Last updated