How Safeheron Secures Users Private Keys
05/05/2023
By Kane
The Web3 industry is unique in that it involves managing a large number of crypto assets, often worth tens or hundreds of millions of dollars, which are stored on the blockchain and authenticated using a unique private key. Whoever possesses the private key is the rightful owner of the assets. Since its inception, Safeheron has pledged to provide customers with 100% ownership and control of their assets.
MPC wallets have been more and more popular in recent years. However, many users may be unfamiliar with MPC self-custodial wallets. This article will introduce Safeheron MPC wallet features, addressing some commonly asked questions.
Why did Safeheron select 3/3 as the signature threshold for its MPC wallet?
The Threshold Signature Scheme (TSS) is a cryptographic technique that safeguards the security of private keys. Safeheron utilizes MPC technology to implement the TSS scheme. For example, a t-of-n threshold indicates that a minimum of t participants out of n are required to complete the signature process when it is necessary. This ensures that the signature remains secure and valid, even in the event of a malicious attack or the failure of some participants.
If the custody provider had selected 2/2, the user would have held one key shard while the provider would have held the other. This arrangement would have resulted in a single point of risk for assets when managing the key shard internally by the provider, which would have made risk control challenging.
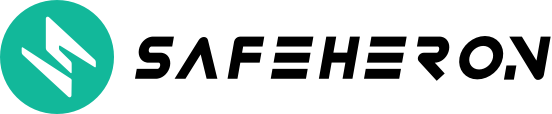
Safeheron's decision to use the 3/3 threshold signature scheme was based on the goal of protecting user private key security. This decision was made with consideration given to the need for client self-custody, as well as to protect against external hackers, internal employee theft, and malicious behavior from third-party cloud providers.
Under this scheme, the client holds one key shard, while Safeheron and a trusted third party each hold one. Safeheron also selects two different cloud service providers that support trusted computing to ensure a higher level of private key security. This approach ensures that a single cloud provider can only access one key shard, making it more difficult for attackers to target the private keys. By separating responsibilities for managers of different key shards and following the Principle of Least Privilege (PoLP) for physical network and system security, Safeheron provides additional security measures to safeguard client assets.
Is an MPC wallet always a self-custodial wallet?
This question can also be phrased differently: Do users of MPC wallets always have full ownership over their wallets?
Of course not, being a self-custodial wallet or not actually is determined by the distribution and control of key shards. Safeheron is a good example of a self-custodial wallet.
Safeheron is confident that the best solution is to ensure users have 100% ownership and control over their funds. This is why Safeheron's MPC protocol uses a 3/3 threshold. The user holds one key shard, Safeheron holds one, and a trusted third party holds the remaining shard. The user's key shard is generated, stored, and used locally using MPC technology. Safeheron and the trusted third party only have access to one key shard each, which does not meet the 3/3 threshold. Thus, Safeheron and the trusted third party cannot use their key shards to control client assets. Only when the user authorizes a transaction and participates in the multi-party computation with his/her key shard can the signature be generated, and assets be transferred. Users can back up all key shards and have full control over their assets even if they leave Safeheron's software and services.
Safeheron's MPC-based self-custodial service minimizes the risk of single-point failure for private keys and guarantees that users have full ownership and control over their assets.
Can some key shards stored in the cloud for an MPC wallet be lost?
The technology behind Safeheron employs a 3/3 MPC threshold scheme, where two key shards are managed and stored by Safeheron and a trusted third party, and the other is generated and stored locally on the user’s device. The two key shards stored in the cloud are generated in a Trusted Execution Environment (TEE), encrypted, and then saved in a database. To ensure the high persistence of the key shard data, Safeheron adopts a multi-cloud and multi-region backup strategy for cloud data to prevent the risk of single-point failure in cloud storage, so that to avoid the loss of key shards in the cloud.
What are the differences between the backup methods for key shards of an MPC wallet and those for regular wallets/hardware wallets?
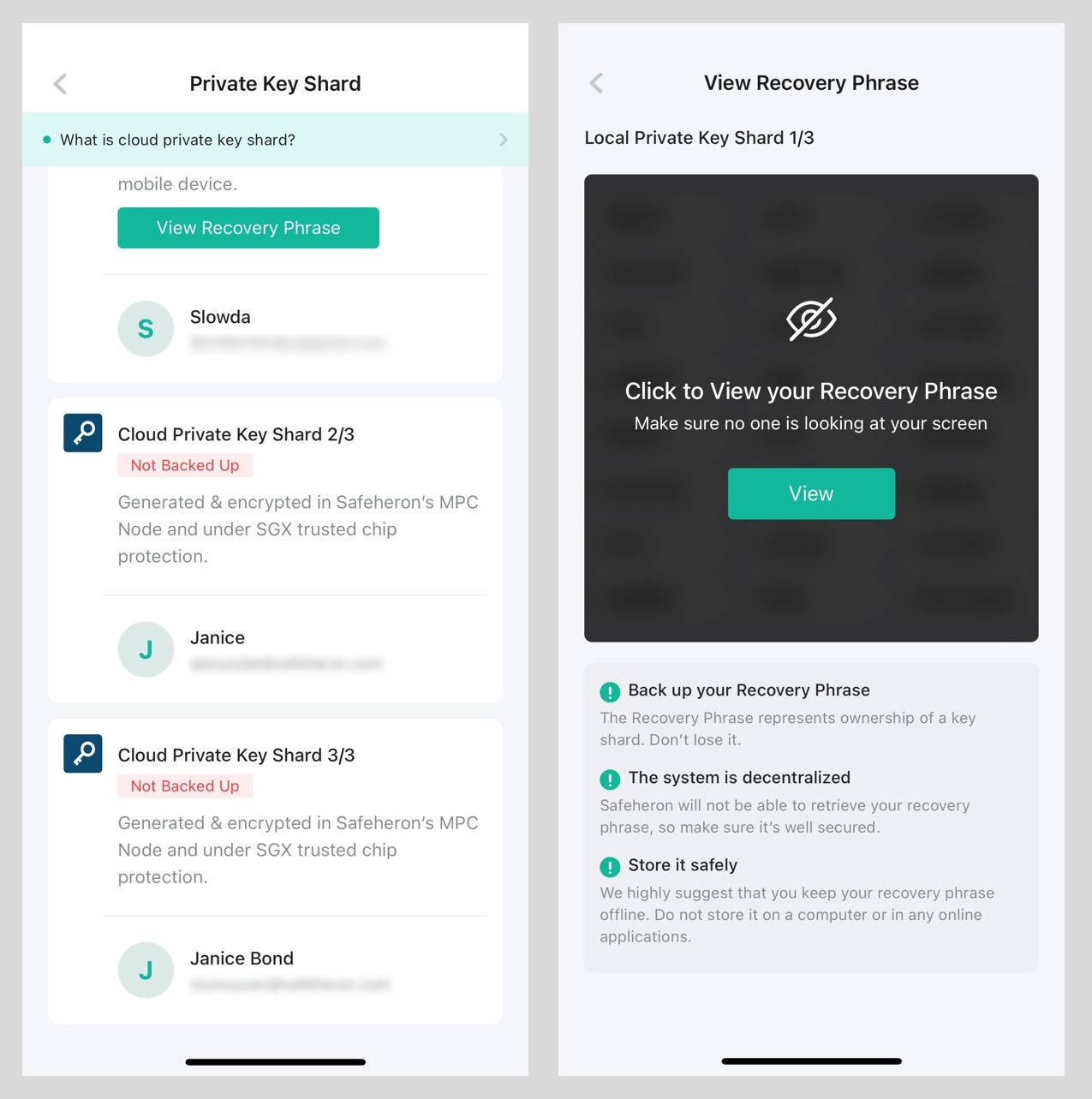
There's not much difference! When it comes to backing up a wallet with Safeheron, it's similar to doing so with a regular or hardware wallet. Users can back up their key shards through recovery phrases, which can be done offline for convenience. Thanks to Safeheron's cryptographic protocols, users don't need to back up Keystore files or other key shard data packages. They can back up their local private key shards and the two cloud-based key shards that correspond to the recovery phrases anytime and anywhere, which is consistent with their backup habits when using wallets. The only difference with a regular wallet is that with Safeheron, users need to back up three sets of recovery phrases instead of just one.
What should I do if Safeheron stops operating?
Don't worry! Safeheron's offline private key recovery tool ensures that users can recover their private keys in any situation, even if Safeheron ceases operations!
Safeheron will require users to back up their key shards and provides an open-source offline tool for private key recovery. After backing up their key shards, even in the event of Safeheron ceasing operation, users can still use the locally backed-up key shards (PS: Safeheron regularly sends wallet files containing BIP44 path to users’ email addresses), and the offline recovery tool can be downloaded and used from GitHub.
Users can install the tool, disconnect their computer from the internet, and enter the three sets of recovery phrases backed up previously, along with the specified BIP44 path wallet file, to recover the private key. The recovered private key can be imported into a regular wallet for normal use.
Offline recovery tool ⬇️
Can beginners use an MPC wallet?
The process of operating an MPC wallet is straightforward, making it easy for beginners to use. With the help of Safeheron's manual, users can quickly get started.
All steps can be completed on a mobile phone, including creating teams, adding members, creating wallets, backing up wallets, viewing receiving addresses, adding whitelist addresses, configuring approval processes, initiating transfers, approving transactions, signing transactions, and viewing transaction history and status.
Safeheron offers a Web Console for customers who prefer to operate on their desktop computers. Web3 interaction is easy, and users with prior experience using MetaMask can use the Safeheron browser extension without any additional learning. The extension can initiate transactions and multiple people can approve them on their mobile devices, resulting in a secure and efficient process.
You can quickly learn about the Safeheron user experience right here ⬇️
Safeheron, as an MPC self-custody service provider, will continue to deliver more industry-related content to accompany users in both traditional and blockchain industries on their journey, moving forward with valuable insights.
Last updated